OneTrust + WordPress UTM Tracking That Respects Consent and Still Works
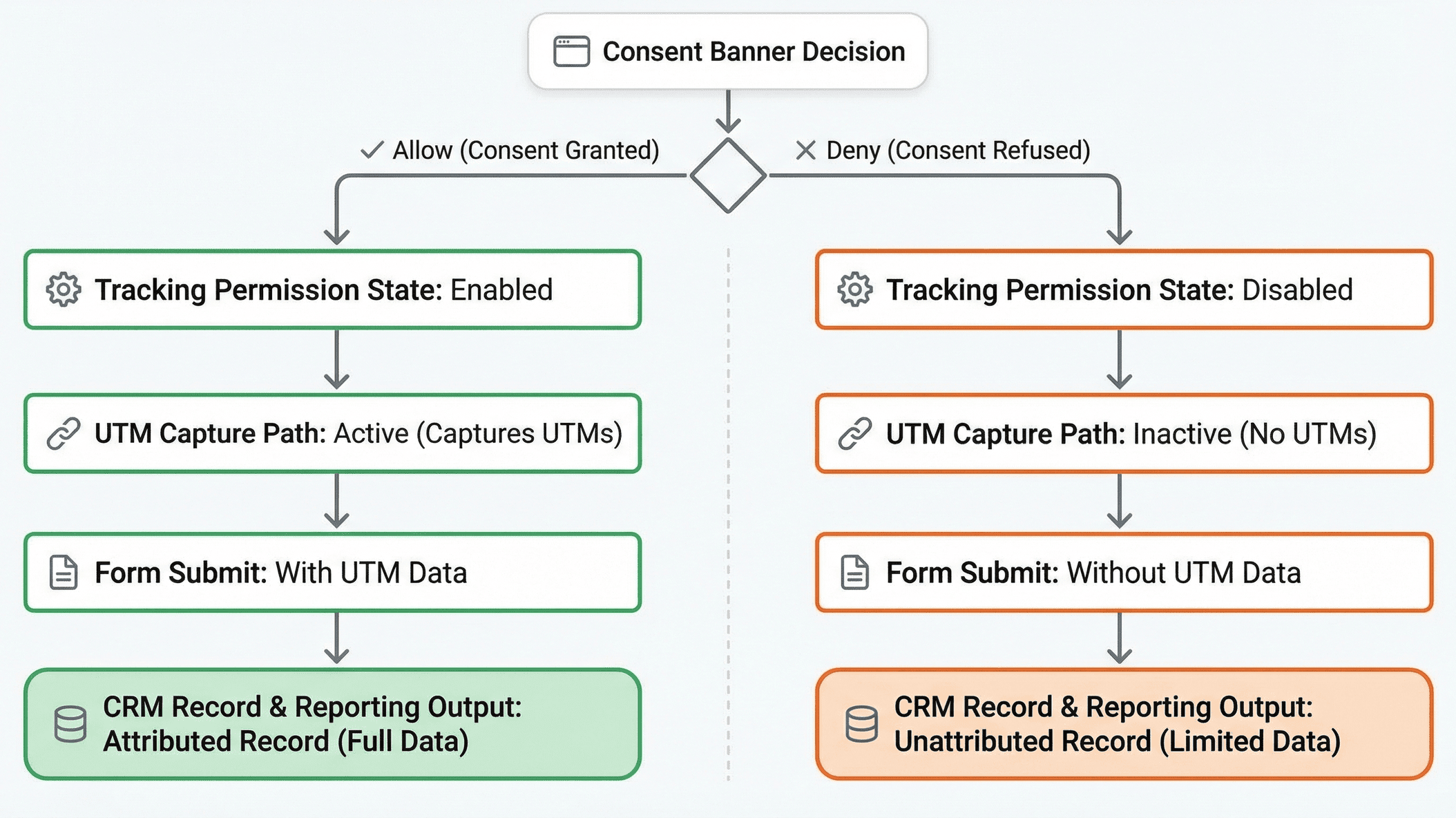
Consent-mode changes should not make attribution unpredictable if your data routing is explicit.
If this sounds familiar
- Attribution quality changes after consent-banner updates.
- OneTrust category state is not wired into downstream automation.
- WordPress plugins rewrite URLs and drop query parameters on some pages.
- Teams cannot explain channel-level reporting drops after compliance changes.
- Consent and growth teams operate from different data assumptions.
These are fixable implementation issues, not random analytics noise.
Consent-aware implementation pattern for WordPress stacks
Make consent state a first-class input
When consent changes, your capture and routing logic must react immediately.
For OneTrust-based setups, wire consent events into your attribution handling workflow.
Split your paths
- Operational path: minimum fields needed for lead ops.
- Marketing path: optional enrichment only when policy permits.
WordPress-specific verification
- Test with cache/CDN enabled and disabled.
- Confirm query params persist through internal redirects.
- Confirm consent-state changes alter routing as expected.
Related reading:
- GDPR Compliant UTM Tracking - UTM Grabber
- UTM Tracking Without Third-Party Cookies - UTM Grabber
- Why Attribution Breaks - UTM Grabber
What this costs when left unresolved
- Teams either over-collect risky data or lose too much signal.
- Channel reports become unstable after policy-related deployments.
- Incident response time rises when routing logic is implicit.
Consent-state blind spots create both compliance risk and bad channel decisions.
What good looks like in practice
- Consent state and attribution fields travel together.
- Routing logic is predictable and auditable.
- Reporting remains useful within policy limits.
When source data is stable, optimization speed improves immediately.
Why this stays broken for many teams
This is exactly why we built UTM Grabber
UTM Grabber helps WordPress teams keep attribution operational while honoring consent controls.
- Consent-state aware capture patterns.
- Stable field schema across WordPress handoffs.
- Operational reporting with lower compliance risk.
Who this implementation is for
- Compliance-aware growth teams.
- WordPress ops owners.
- Organizations with stricter privacy requirements.
If attribution quality affects how you allocate budget, this is the right workflow.
What real users are saying
/#schedule-demo No need to rebuild your whole stack.
